For business in change
Trend Micro hybrid cloud
Trend Micro’s Cloud One security platform is a tool that provides the breadth, depth and innovation required to manage the Cloud Security needs of today and the future.
About Cloud One
Hybrid Cloud security
Trend Micro’s Cloud One security platform is a tool that provides the breadth, depth and innovation required to manage the Cloud Security needs of today and the future. The server and application protection software bundlesthe security of virtual, cloud computing and traditional data centres and helps organisations to prevent data breaches and business disruptions, ensures compliance with key regulations and standards including PCI and helps reduce operational costs when the economic situation requires such.
The Deep Security solution enables systems to defend themselves and is optimised in such a way that confidential data is optimally protected and application availability is guaranteed.
Depending on the licences that have been activated, the following modules may or may not be available in the environment: anti-malware and web reputation, firewall and intrusion prevention, integrity monitoring and application control, and log inspection. Products are available in agentless and agent-based options that can all be managed from a single console in both virtual and cloud server deployments.
Trend Micro Cloud One Services
all-in-one solution
Workload security
Secure data centres, cloud and containers without compromising on performance or security, with an easy-to-use, uniform SaaS solution
.
Network security
Powerful and seamless network layer protection, detection and threat disruption for a multi-cloud environment.

Container security
Simplify security for Cloud Native applications with advanced container image scanning, policy-based admission control and container runtime protection.
File storage security
Optimal protection of Cloud file / object storage services that supply Cloud Native application architectures.

application security
Detection and protection of modern applications and APIs that are built for container, serverless and other computing platforms.
open source security
Get a handle on open-source code vulnerabilities, enhance visibility and set priorities in an efficient and convenient manner.
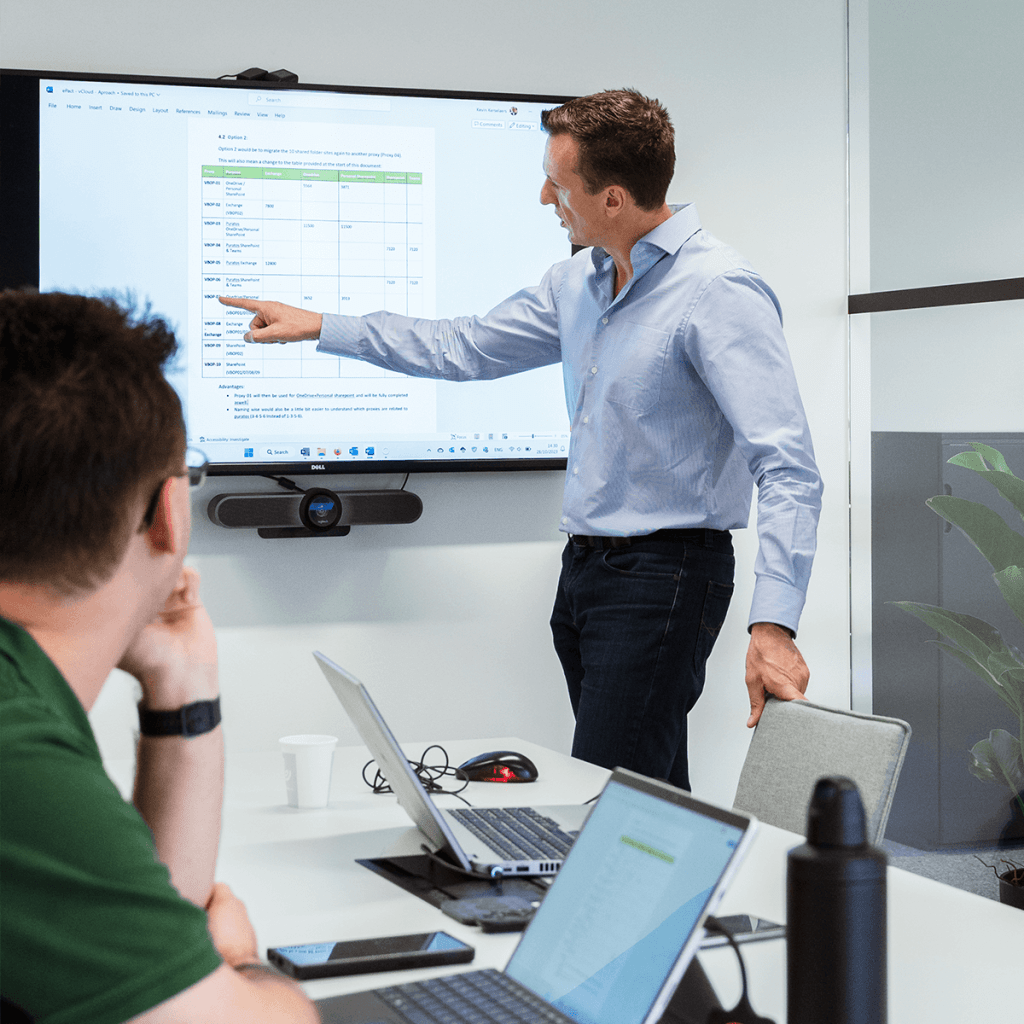
Why ePact
Installation and configuration of Trend Micro CLOUD One
We begin the project with a kick-off meeting in which we record all the objectives and requirements of all stakeholders. In the next phase, we begin to implement and configure the proposed solution(s) and prepare the environment for deployment of the pilot systems. These are then reviewed and once approved they are rolled out to the full infrastructure under the necessary guidance. In the last phase, we undertake a final check and provide all the teams involved with training.
After the final roll-out, we recommend that an engineer check the environment on a monthly basis for updates and critically review the existing policies. If necessary, the engineer can personalise settings and assist in the deployment of the Cloud One portfolio.
Trend Micro Cloud One
All-in-one cloud security from development to runtime to response

Automated
Save time, gain visibility. Automated deployment and discovery lead to operational efficiencies and accelerated, streamlined compliance.

Flexible
Builder’s choice. You choose the cloud, the platforms and the tools, and we leverage our turnkey integrations and broad APIs, leaving you free you to procure the way you want and deploy the way you need.

All-in-one
One tool that has the breadth, depth, and innovation required to meet and manage your cloud security needs today and in the future.
Get started on your digital transformation today
We would be happy to learn more about your business during a no-obligation meeting.
